Assess and expose
Operators need to know what they own, what is exposed, what is obsolete, and what suppliers can reach.
Critical infrastructure is entering a security era where cyber defense is no longer an IT add-on. It is part of the asset itself: physically strong, digitally resilient, operationally recoverable, AI-aware, and safe under stress.
The stronger question
Can we remove the attacker's opportunity before the attack becomes possible?
Download the 31-page report on OT exposure, AI governance, supplier trust, secure edge, and operational recovery.
Critical infrastructure used to be protected by distance. A plant had control rooms. A pipeline had field equipment. A substation had local controls. A water facility had isolated systems.
Now the asset is connected through remote access, sensors, dashboards, contractors, smart meters, edge devices, vendor portals, AI tools, and supply-chain software. That connectivity creates efficiency. It also creates opportunity for attackers who can convert one weak login, exposed device, or supplier path into operational pressure.
The attacker does not care which department owns the weakness. The customer experiences the outage. The operator experiences the safety pressure. Leadership experiences the trust, regulatory, and financial damage.
The shift
Distance is no longer a defense when assets depend on remote access, suppliers, dashboards, and AI tools.
One weak path can become operational pressure.
Modern attack flow
Attackers do not need a dramatic opening. They need a reachable system, a trusted account, or a supplier path they can turn into pressure.
An internet-connected OT device, remote access point, supplier login, or unpatched system is discovered.
Attackers use default passwords, stolen credentials, phishing, or vendor access.
They cross from IT into OT, or from one supplier into many customers.
They study operations, backup routines, shift patterns, and failure points.
Ransomware, data theft, process disruption, payment fraud, or public embarrassment is timed for impact.
Downtime, safety risk, regulatory pressure, lost revenue, and loss of trust become the business result.
Preemptive cyber defense is becoming a major business opportunity in infrastructure because customers need continuity, not just more cybersecurity tools.
A hospital cannot pause care. A water utility cannot lose control. A port cannot stop moving goods. A power operator cannot guess whether a control signal is real. The winning customers will make attacks harder, slower, less profitable, easier to detect, and less damaging when attempted.
Cyber defense for critical infrastructure is moving from response spending to resilience investment.
Source
Operators need to know what they own, what is exposed, what is obsolete, and what suppliers can reach.
New power, water, telecom, transport, and industrial projects need cyber requirements in design, procurement, commissioning, and handover.
Remote operations, sensors, dashboards, and AI analytics require identity, segmentation, logging, and controlled access.
Continuity plans must cover manual operations, restore testing, offline backups, alternate communications, and leadership decisions.
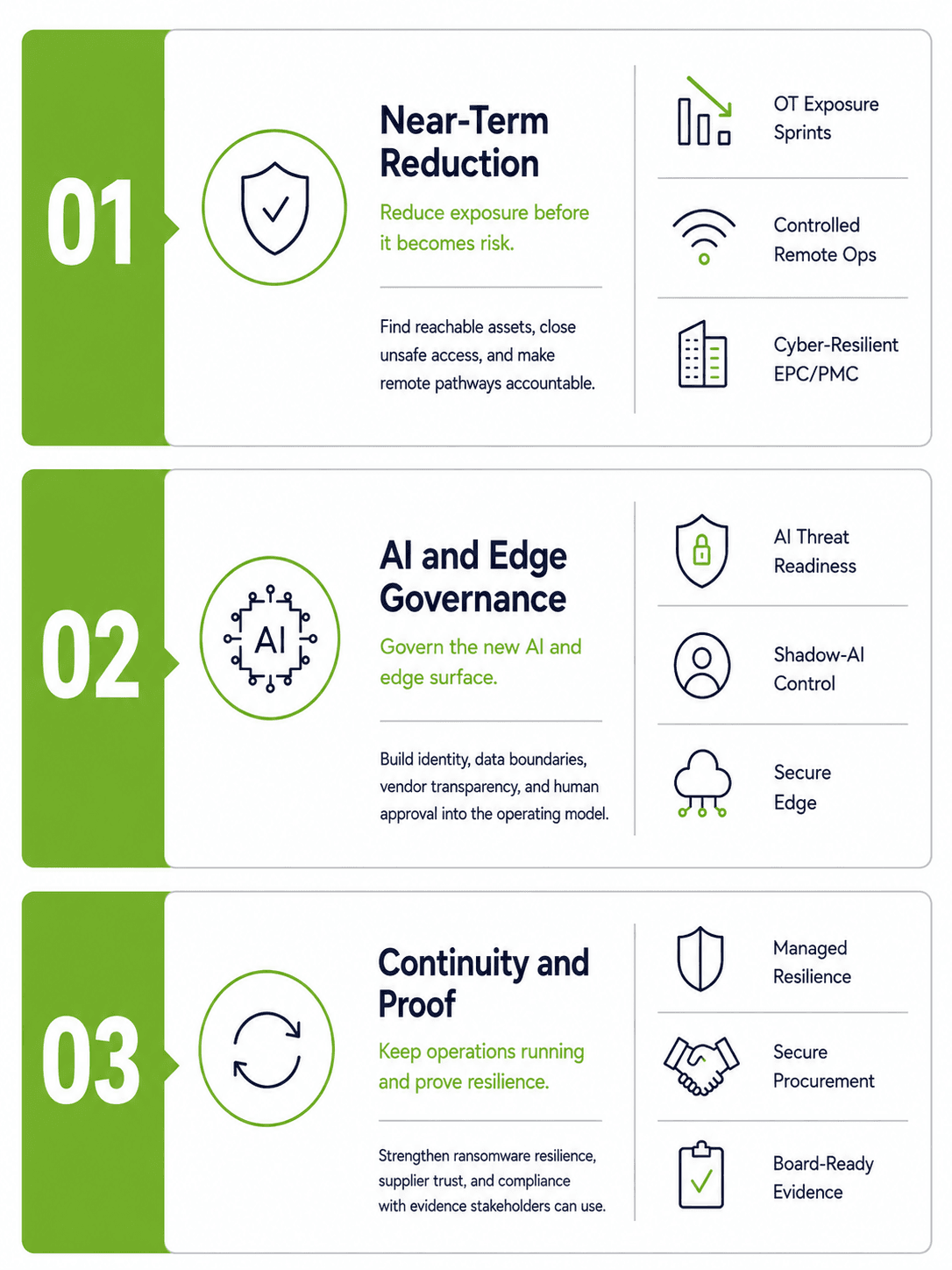
Near-term reduction
Reduce exposure first. The fastest value comes from knowing what is reachable, closing unsafe access, and making every necessary access path accountable through work such as OT Exposure Reduction Sprints, Cyber-resilient EPC and PMC, Controlled Remote Operations.
AI and edge governance
Govern the new surface. AI tools, shadow AI, edge devices, and AI-enabled OT systems can improve performance, but only if identity, data boundaries, vendor transparency, and human approval are built into the operating model across AI Threat Readiness, AI Governance and Shadow-AI Control, Safe AI-in-OT Integration, Secure Edge Infrastructure.
Protect continuity and turn posture into proof. Ransomware resilience, secure procurement, supplier trust, compliance, cyber-physical design, managed resilience, and role-specific training all point to the same commercial need: customers must preserve operations under pressure and produce evidence that boards, lenders, insurers, regulators, and operators can use.
The biggest cyber opportunity in infrastructure may be the simplest: stop adding cybersecurity after the asset is already built.
Cybersecurity should be visible before equipment is ordered, before vendors are selected, before remote access is granted, before commissioning begins, and before operators inherit the system.
Project acceptance standard
Cybersecurity becomes part of the standard for safety, quality, cost, delivery, procurement, and commissioning.
BG Titan brochureWhat changes by phase
Cybersecurity should create a practical record at every handoff: requirements, supplier commitments, controlled site access, tested recovery, and operating evidence.
Define cybersecurity zones, conduits, remote access rules, data flows, backup requirements, and manual operating assumptions.
Require secure-by-default devices, update commitments, vulnerability disclosure, lifecycle support, and supplier access controls.
Control temporary access, contractor laptops, shared credentials, engineering workstations, portable media, and undocumented changes.
Test segmentation, backups, logging, fail-safe behavior, account ownership, password changes, and operator handover.
Maintain asset inventories, patch windows, supplier records, remote access logs, restore tests, and incident playbooks.
A practical view of the controls, procurement rules, access models, and recovery evidence critical infrastructure customers need now.
Many industrial systems were designed for reliability, not internet exposure. That was acceptable when they were isolated. It is dangerous when they are searchable, remotely reachable, or connected through poorly controlled support paths.
For many operators, the first cyber win is not advanced AI. It is closing the doors that should never have been open.
Source
First sprint outcome
Find what is visible, close what should not be reachable, and document the before-and-after exposure picture.
Day 30
Day 60
Day 90
Remote access is not the enemy. Uncontrolled remote access is.
Remote access usually does not fail all at once. It grows informally through one vendor account, one emergency exception, one old VPN, one shared password, one forgotten integration, and one permanent side door. Every remote session into critical infrastructure should be approved before it starts, limited to what is needed, recorded while it happens, revoked when it ends, and reviewed when risk changes.
Access standard
No standing side doors into critical operations.
Verify the request, broker the session, record the work, and expire access when the job is done.
Before
Confirm the user, device, system, purpose, and time window.
During
Use a brokered session instead of an open tunnel or shared credential.
After
Revoke access, keep the record, and review the session when risk changes.
AI changes cyber risk because it improves the attacker's economics. It helps attackers research faster, write better phishing messages, translate scams, generate code, impersonate voices and brands, and process stolen data at greater scale.
AI is also being adopted inside organizations faster than many security and compliance teams can govern it. For critical infrastructure, AI governance must control what people actually do during procurement, maintenance, reporting, planning, analytics, and emergency response.
Sources
Risk equation
Volume
More attempts reach more people.
Trust
Messages become harder to dismiss.
Speed
Fraud and intrusion pressure arrive sooner.
The Inventory
Map tools, models, copilots, chatbots, vendors, and automation features before they become invisible dependencies.
The Approval Path
Define what data can be uploaded, who can connect AI tools, and which actions require human approval.
The Fraud Check
Verify payment changes, executive instructions, vendor requests, and emergency actions against AI-enabled deception.
The Test Bed
Use non-production or simulated testing before AI touches operational environments.
The Fallback
Keep known-good automation or manual control available when AI behavior is uncertain.
The Evidence Layer
Log inputs, outputs, overrides, exceptions, and vendor behavior for review.
Strong early use cases
The safest early AI deployments are narrow and assistive: predictive maintenance, anomaly detection, energy optimization, operator assistance, and document intelligence. These use cases can improve performance without handing unsafe control to a model.
The design test is simple: AI should help operators see more clearly, decide with better context, and fall back to known-good processes when confidence drops.
Ransomware has become an industrial business model. Attackers do not need to physically damage a facility to create leverage; they can encrypt systems, steal data, disrupt scheduling, interrupt payments, pressure executives, and exploit regulatory fears.
The strongest strategy is not only to stop malware. It is to make ransomware less profitable by reducing the attacker's ability to spread, encrypt, extort, and pressure the business.
Recovery standard
Continue essential service while systems are isolated, restored, and verified.
Backups, segmentation, manual operations, and decision playbooks must work together before the incident starts.
Denial architecture
Limit spread, encryption, and pressure.
Spread
Segmentation, least privilege, vendor limits.
Encrypt
Offline backups, restore tests, manual operations.
Pressure
Phishing-resistant access, executive playbooks.
Get the full BG Titan Group framework for reducing attacker opportunity across design, procurement, operations, recovery, AI, and supplier ecosystems.
Critical infrastructure relies on equipment manufacturers, system integrators, maintenance contractors, cloud platforms, telecom providers, software vendors, security vendors, and specialist engineers.
Every supplier can improve performance. Every supplier can also create risk. Procurement must move from "Can you deliver the equipment?" to "Can you deliver equipment we can safely operate, update, monitor, and recover?"
Edge question
Procurement should qualify supplier cyber posture before selection, require secure-by-default equipment, define patch and disclosure commitments, control vendor remote access, and make acceptance testing part of handover.
Edge devices need identity, segmentation by function, secure update paths, local resilience when cloud connectivity degrades, controlled outbound data movement, and zero-trust access for users, vendors, and services.
The practical filter is simple: do not accept equipment or connectivity that cannot be safely operated, updated, monitored, and recovered for the life of the asset.
Regulators, insurers, boards, lenders, and public-sector stakeholders increasingly want evidence, not reassurance. Compliance is often treated as paperwork, but in critical infrastructure it should become a path to resilience.
Cybersecurity is also becoming a transaction risk. Weak cyber posture can affect financing confidence, insurance terms, project valuation, government approvals, supplier selection, post-acquisition integration, and operational readiness.
Shared risk
The control room and the boardroom now share the same risk.
A cyber incident can become a physical, operational, financial, legal, political, and public-trust incident.
Asset inventories
Risk assessments
Supplier due diligence
Incident-response procedures
Backup and restore tests
Access-control records
Training records
Governance minutes
Audit logs
Business-continuity exercises
Asset and architecture review
Material risk assessment
Supplier and contract review
Recovery capability review
AI and data review
Remediation budget
Insurer and lender pack
Critical infrastructure cybersecurity often falls into a gap. IT understands networks and identity. OT understands operations and safety. Engineering understands the asset. Procurement understands suppliers. Executives own risk. No single group sees everything.
Customers need more than tools. They need operating models with roles, decision rights, escalation paths, training, supplier responsibilities, and executive reporting.
The objective is to avoid making a ransomware event, supplier compromise, or AI misuse incident the first time the organization learns how to work together.
Risk reviews across operations, IT, suppliers, and leadership.
Access audits for vendors, maintenance windows, emergency access, and session logs.
Recovery exercises for ransomware, supplier compromise, remote-access abuse, AI misuse, and OT disruption.
Supplier reassessments and executive cyber-resilience briefings.
Preemptive cyber defense is not about predicting every attack. It is about removing the easy paths attackers depend on.
BG Titan sees denial-of-opportunity as a business and infrastructure strategy: every project, modernization, procurement decision, connectivity rollout, AI deployment, and supplier relationship should reduce attacker opportunity rather than add to it.
What this does to the attacker
Denial-of-opportunity removes the easy paths attackers depend on, then makes abnormal behavior more visible and recovery more credible under pressure.
01
Know the asset + reduce exposure
Inventory what exists, then remove internet-facing OT, default passwords, unnecessary services, weak remote access, and dormant accounts so attackers have fewer usable openings.
02
Control identity + segment and contain
Verify users, devices, vendors, and service accounts, then segment systems so one compromise cannot become an enterprise-wide or site-wide crisis.
03
Watch behavior + govern new surfaces
Detect unusual access, abnormal process behavior, suspicious data movement, supplier anomalies, and emerging AI or vendor surfaces before they become hidden dependencies.
04
Rehearse recovery + govern decisions
Test backups, manual operations, communications, and decision-making so the organization can recover, communicate, and continue essential service under pressure.
These questions are for boards, ministries, utilities, developers, operators, financiers, insurers, and project teams. They are not a technical checklist; they are a decision agenda.
If the answer is unknown, exposure may already exist.
Access should be approved, logged, limited, and revocable.
Segmentation should prevent corporate incidents from becoming operational crises.
Default passwords remain one of the most preventable risks.
Manual capability must be realistic and tested.
A backup that has never been restored is an assumption, not a recovery capability.
Shadow AI, embedded AI features, and vendor AI tools must be governed.
Procurement should verify security before equipment and software are accepted.
Slow decision-making can deepen operational damage.
Evidence is becoming part of the market.
A customer does not need every answer perfectly on day one. Unanswered questions should become funded workstreams.
Download the full BG Titan Group report with the threat model, opportunity radar, 30-60-90 exposure path, secure procurement checklist, AI-in-OT guardrails, and resilience operating model.
The future of critical infrastructure is connected: more sensors, edge computing, AI, remote operations, cloud analytics, supplier integration, automation, and regulatory reporting. That future is powerful only when resilience is designed into the asset from the beginning.
Connectivity will keep expanding across field equipment, analytics, suppliers, operators, and AI-enabled services. If cybersecurity arrives after construction, procurement, commissioning, or AI adoption, the operating model inherits avoidable fragility.
BG Titan can bring cyber resilience into concept and feasibility, project development, financing, EPC and PMC/PMT, procurement, technology solutions, commissioning, operational readiness, risk management, and continuity planning.